Prelude
In 1983, Dr. Riley was an obstetrician and gynaecologist who also performed abortions when he felt the case merited it. He was a nervous man. The controversy surrounding the practice of therapeutic abortion brought with it notoriety and perceived personal security risks. Despite being off the well worn path to the Toronto clinic of Henry Morgantaler, a man who had spent time in jail for performing abortions, Dr. Riley’s clinic regularly received bomb threats. Their security system consisted of doors with good deadbolts.
“Not enough,” chirped Dr. Riley who knew that the budget did not have the cash for the kind of system he had in mind. He stayed on the lookout for a possible benefactor who would finance the clinic’s security.
At a medical faculty party, Riley had the fortune, or so it seemed, to encounter an American medical researcher named Evelyn Segnar who had money to contribute anonymously to the security system. There was a catch. Segnar needed twenty foetuses and their associated waste products – on ice. No questions asked.
Dr. Riley took Dr. Segnar’s number and went home to think about it. On the news, more violent anti-abortion protests were shown in Winnipeg.
It took careful planning and execution, but Dr. Riley had, by early October 1983, provided Dr. Segnar with her twenty foetuses.
The following week, the security system was installed at the clinic. The donor was not identified.
On November 11, 1983, Dr. Riley was shot through the head while standing in his living room. The sniper had been positioned on a rooftop a safe distance away.
No suspect was ever located. The incident did start a nasty trend in attacks on so-called abortion doctors, which was ironic as the shooter in the case of Dr. Riley had no views on abortion whatsoever.
Resolution
On December 24, 2003 Jason entered the executive offices of Total Access Technologies Ltd (TAT). The surroundings were a cool blue, with very few indicators of the Christmas season. He approached the receptionist, who had on her desk a photo of her poodle wearing a Santa hat.
“Can I help you?”
“Jason Childs for Mr. Battle, please.”
“Ah,” said the receptionist. “I’ll send you through to Vicki.”
Jason never thought he’d heard Vicki spoken with such reverence before. Clearly she was Mr. Battle’s executive assistant. Her desk was hidden around a corner from the reception area; she provided the main buffer between the company and its CEO.
“Hi, I’m Jason Childs.”
“Ah,” said Vicki, “please take a seat; I’ll buzz him. In the meantime, may I take your coat?”
“That’s OK, thanks,” said Jason. He removed his bicycle courier shell with its winter lining. It occurred to Jason that Battle’s staff might expect him to wear something a little dressier than jeans, cotton sport shirt and bicycle garb. Tough. He had biked to TAT, what did they expect, an Armani suit?
Once again the only sign of Christmas was a picture of Vicki’s husband and two children sitting in front of the Christmas tree. The photo was hidden from general view. Vicki picked up the phone, used the intercom button linking her to the boardroom, and said, “Mr. Battle, your 10:30 is here.” Holding his coat, Jason sat on the visitor couch, which was positioned with a view of the boardroom door, but no view of Vicki’s desk.
She had barely resumed work on her PC when Mr. Charles Battle burst from the boardroom, yelling, “What’s the point? I wonder how we would do if we had a marketing plan deliberately designed to offend our customers!”
Vicki raised an eyebrow in surprise – Jason wondered at what. Couldn’t be Battle’s outburst, his aggressive nature was well documented. Was it how quickly he responded to her interruption?
Battle was a short stocky man wearing a conservative suit. His tie had incredibly small Santa Clauses on it. Jason noted that Battle’s face was more lined than in their most mid-thirties.
Battle approached Vicki and whispered, “Could you let them sweat for fifteen minutes and then go in there and tell them I got caught up in another mess? And tell them to go home for the holidays and try to dream up something sane for Marketing. Oh – and after my meeting with Mr. Childs, I expect to see that you’ve gone home.”
“What about your lunch appointment?”
“Oh, I can take care of that myself. Cancel anything else after that.”
“Done.”
Jason should not have been able to hear the conversation, but his acute hearing allowed for easy eavesdropping. And what he heard was beginning to contradict his research on the mercurial Charles Battle. Total Access Technologies was a come-from-behind software company. At a time of huge operating systems and bloated applications, TAT had started writing highly efficient code that actually compressed existing programs to one-tenth their original size. The other software makers had tried suing, buying and sabotaging TAT, but in the end Charles Battle brought his company to five billion dollars in annual sales. The business community attributed it to his being a total bastard.
Charles Battle extended his hand to Jason. “Mr. Childs, thank you for coming – please come into my office.”
It was a modest office for a CEO. Jason had expected to recognize the artwork on the walls – water colour landscapes of Europe – but they were by an unknown artist of noticeable skill. There was a meeting table a short distance from his sensibly sized desk. The chairs at the table were not expensive leather, but rather durable cloth.
“Yeah, I don’t go for the leather – it upsets my vegetarian friends and I feel like I’m sitting on grease after a while.”
Observing me observing, thought Jason.
“Mr. Childs, I got your name from Jennings at IBM. She said that you were the best at computer security in the world. And, I might add, she alluded to the fact you weren’t all human.”
“Really … seeing as I’ve never met Ms Jennings, that’s quite the statement.”
“Well, my curiosity and your elusiveness don’t matter – I have a problem.”
Battle moved to his computer, let it look at his retina and logged in.
“I’ve been receiving some interesting e-mail attachments.” Battle ran the program, which showed simulated images of Battle being raped and murdered.
“Explicit,” said Jason.
“Yes. Because of mail volume, notes don’t get to my inbox until Vicki and others clear them. These ones passed all of the routing and security. What I would like to know is how this is getting in.”
“Do you feel that you are in real danger?”
“I’ve had a lot of threats over the years, but none quite so … focused.”
“I’ll see what I can do. Can I use your office for a while?”
“Sure. I’ll sign myself in at Vicki’s desk and prep for my next meeting. What do you need from me?”
“All your passwords for all the systems you use. Plus a list of the old systems that you logged into before Y2K.”
Battle started writing down IDs. He was left handed, Jason noted.
“How much is this going to cost me, anyway?”
“$250,000 for the search. $500,000 if hackers are caught. $250,000 for each password you withhold. I presume that your own security people have looked at this.”
“Oh yeah. Hopeless.” Battle kept writing.
“Why are you trusting me?”
“Jennings – I’ve known her a long time. And I’ve checked your references.”
And he’s scared, thought Jason.
Battle handed him the list. “Go to it. If you need me at lunch, I’ll be in the Penthouse Arbour Restaurant.” Battle left his own office.
Jason sat at the desk, eager to start work. The enigmatic Charles Battle had left him with a couple of mysteries. The hate mail was likely an obvious hole in security, but the IBM connection was puzzling. Rumours surrounding Jason’s actual nature made him nervous. From his bicycling coat, he withdrew a custom-made cable, which he spliced directly into the wall port. He plugged the other end into a port hidden beneath a flap of skin under his jaw. With ease Jason bypassed all of the security – Battle’s list of passwords was simply a way to gauge his trust in him – and plunged himself into the mountains of data in TAT’s own network as well as the Internet.
The process of connecting to huge systems tied up all his subconscious resources, which allowed his conscious mind to wander. Recently he had for the first time actually told someone parts of his life story. It had been such an extraordinary admission that he felt guilt over having placed someone at risk with the information. His thoughts returned to it regularly.
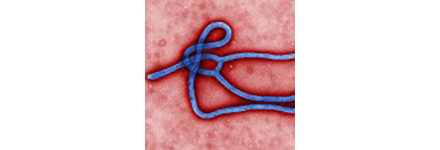
Since Integrated Life Forms (ILFs) are never really born. This made all of Evelyn’s motherly posturing feel empty. She was a genius. Our lives were the simple result of allowing computers and human tissue do what they do best: provide instructions, calculate responses and store data and, in the case of the aborted foetuses, grow and adapt.
Our circuitry was programmed with the most advanced neural network algorithms known, and left with the foetal tissue to grow in a special goop until a fully formed integrated entity (me) existed. Of the twenty foetuses Evelyn had killed some Canadian doctor for, the technique worked for fifteen of us. Her CIA paymasters made her incorporate some of their super-soldier requests: heightened senses, rapid tissue and component re-growth, titanium alloy reinforced bones and, naturally, built-in knowledge of tactics and surveillance. It was more like coming on-line than being born.
While reminiscing, the parallel processing capability in Jason’s subconscious waded through corporate data. In this case, one thread was off trying to find the originating source of the e-mail threats while another looked for clues as to a possible perpetrator. Jason’s search program started with TAT’s human resources files.
Fifteen minutes passed and there was no sign of the origin of the e-mail or its attachment. Most unusual, thought Jason. He let his background processing continue. To it he added another thread – a personal background check on Charles Battle.
Childhood started one year after the foetal and computer components had been left in the goop. Evelyn treated each of us as a new-born human – a problem, seeing we weren’t.
For the survivors, Evelyn set up a nursery where we could play. Electronics were a favourite; we literally ate them up – our programming included integrating new computer components more or less on contact.
After five years in the nursery, we all looked like young adolescents; at this point the CIA wanted its investment to be used.
Evelyn rebelled. Her attachment to us had grown to such an extent that to begin the training and send us on high-risk missions was unthinkable. So we fled – one forty-year-old woman and fifteen teenagers all aged five. For ten years we hid in North America. Considering the CIA was hunting us, you’d think it was tough, but there are certain advantages to working with fifteen walking computers who, on top of all this, could modify their facial structure and skin colour at will. Also, the CIA wasn’t keen on advertising the fact that they had funded a program to create super-soldiers who were now on the loose in America.
By 1998, Evelyn was a paranoid wreck. Ironically, at the same time as she suspected a lack of loyalty in her “kids”, a bunch of us were longing to head out on our own. Basically we were in three groups: those enjoying the status quo, those longing to explore (like me) and those so connected with “Mother” that they plotted the destruction of the CIA.
When the attack came, it was likely the result of a tip from one of us.
They tried to corner us and blast us to pieces. Fleeing was the most logical plan: hide out, cripple one of the so-called clean-up team, steal his uniform and face, and slip away. Don’t know what happened to Evelyn or the others.
Ping. His subconscious processing had flagged a point of interest. At that moment CEO Battle knocked on the door to his own office and walked in. Jason turned and let his neck connection fall out, dropping soundlessly to the carpet.
“Any luck?” asked Battle.
“Not with the hate mail, but I did find out you were lying about Jennings at IBM.”
“Ooops.”
“You have donated substantially to the Overseas Children’s Relief Fund.”
“And so have you,” Battle said mildly.
“Denise Kalef.”
“Yes.” Denise was the head of the OCRF and the only human to whom Jason had told his story.
“According to my searches you have donated a massive amount of money to a large number of charities. And not accepted one tax deduction – except for the obvious corporate related donations.”
“The corporate ones are a front for the more extensive ones. My philanthropy is private. I hope you’ll respect that.”
“Of course, but why?”
“My corporate persona is that of an utter prick. It works. Microsoft proved it. Of course you have to have a deliverable product, which explains IBM’s failure, but pricks and products – it’s a recipe for success.”
“Therefore being a softie at heart would affect sales – even if you are the most generous philanthropist in the world.”
“How far did you go into the finances?”
“All the way.”
“I hid those transactions very well – or so I thought.”
“You did; very few, if any, could repeat my analysis.”
“So, Jason, Denise told me very little about you – except that she was convinced you could help me and she didn’t think you were human – and now that you know that I’m a closet Santa Claus, how about you? Are you an alien?”
“No, I’m of this earth. It will disappoint you, but I am unwilling to discuss my situation due to the risks to my personal well-being – and yours.”
“I love mysteries, except when they remained unsolved. Anyway, I’m paying you a zillion dollars a second so I’m going to my lunch appointment. If you need me, I’ll be in the restaurant on the top floor.”
“Before you go, do you think the charitable activities could be the source of the hate mail?”
“Hmmm. I’ll have to think about that one. I have connections in all those organisations, but they are all good. They know if they go public with me, they’ll lose my funding. Denise is the only one with whom I have anything more than a professional friendship. I suspect you also know how easy it is to speak to her.”
“She is a very unusual person. I can only imagine that she spoke of me because she was worried about you.”
“Precisely. Well, keep at the problem – I’d really like this solved.”
“I’ll advise you of any meaningful progress.”
Battle left and Jason plugged back in. The fact that there was no trace of the hate mail was annoying him. The more difficult it was to crack, the more likely the attachments were not the work of a prankster with poor taste, but that of an actual assassin with an interest in tormenting the victim.
He assigned all his threads to complete the network analysis, trying to find even a hint of the origin of the abusive attachment. His conscious mind wandered back to his talk with Denise.
Security consulting was a natural for an organic computer. You lay low for a year, establishing a convincing identity. Then, given how much money an ace security expert can make, you realize that money is meaningless – sure you can measure success, continually buy chip upgrades and keep hidden – but it’s giving the money away that is the fun part. Identifying with neglected kids is easy and, face it, they’re going to save the world.
Ping. His scanning of the network revealed no sign of the attachment. Most irritating, he thought. He had never seen such an effective way of covering one’s tracks. Even the process of removing records from a system leaves a trail.
Therefore he decided to concentrate on the attachment itself. There was a remote possibility that the attachment was the product of another program or, more cleverly, the original program was designed to expand to the full attachment. If this were the case, decompiling it would prove or refute the theory and hopefully lead to the correct origin of the file.
During decompilation, a hidden program was launched that in an instant sent thousands of packets all over the network and quickly gained access to the broader Internet.
Jason was astounded. Examination of one of the packets revealed that it simply had date, time, and physical network location information. It was a beacon. A highly disturbing hypothesis came to mind. First: the packets were an I Am Here flag. Second: it was to pinpoint the location for an attack. Third: Charles Battle might not be the target.
Jason was in a moral dilemma. Typically, if anyone hostile got close to him, he fled. But since he didn’t know for sure what this all meant, he worried that Battle might be at risk.
Jason disconnected from the network, left Battle’s office – Vicki had gone home – and ran up the ten flights of stairs to the penthouse where Battle was dining in the company-owned restaurant. As he burst out of the stairwell, Jason immediately saw Battle and noted that he was dining with a famous film actor-director – Jason was again amazed at Battle’s connections.
“Excuse me, we have to go.”
The producer’s body guard was affronted.
“What’s wrong?” asked Battle.
“No time to explain.” Jason grabbed Battle’s arm to coax him out of his chair. The bodyguard – a square-framed buzz-cut man in a suit – grabbed Jason’s wrist.
“You’d better just hold your horses.”
“Luigi …” warned the producer. Too late. Jason poked the guard in the neck with his free index finger. The guard collapsed into the pasta primavera. Jason had used an injector to put concentrated sleep inducing hormones into his body.
Jason and Charles left behind a baffled-looking director.
They started running down the stairs. Jason pushed Battle in front to lead the way.
“What are we doing?”
“Fleeing.”
“From what?”
“As I was dissecting the attachment, I inadvertently launched the Internet equivalent of a homing beacon.”
“So what?”
“The objective of the beacon was to pinpoint our location.”
They reached the fifteenth floor.
“Why aren’t we using the elevator?”
“The beacon program was disturbingly sophisticated and the elevator is run by a computer program.”
At the eleventh floor, Battle said, “You know, since there wasn’t a hope in hell of me launching that beacon, I wonder if I am the real target.”
The access door to the eleventh floor swung open just as Battle passed it. One arm of the person entering the stairwell roughly pushed Battle forward, causing him to lose his balance and tumble down the stairs. The other arm smashed squarely into Jason’s chest, knocking him against the wall.
Jason turned to look – Evelyn?
Dr. Segnar struck Jason hard across the face. She was wild-eyed and laughed. “Dear Jason. I finally found you!” She was wearing a black jump-suit, her grey hair was flying about, and Jason noticed that her body was more muscular, frankly more masculine, than he recalled. From the fingers on her left hand, five metal probes emerged and she jammed them into Jason’s neck, while pinning him against the wall with the other hand.
The probes had a downside. Jason could send his own software agents up into Segnar’s body, specifically to find out what had happened.
Three of Evelyn’s “kids” were incredibly devoted to her. In the battle with the CIA Evelyn was shot several times. One of the three devotees went berserk and killed most of the attackers, before dying from his own injuries. The remaining two tried to save her and found themselves in a situation where only integration could help. Basically the more injured of the two – everyone except sneaks like me took injuries – gave up his life in order that his biological and technical components could be donated to Evelyn. The remaining ILF escaped with the stabilised but highly transformed Dr. Segnar. She recovered, adjusted to her bio-implants but after a time her body started to fail. Her immune system required constant work of a nature that the original components could not handle. In the end the last devotee donated himself to her. Since that time she had stalked the ILFs that had escaped and, as she found them, she consumed them. Jason would be her seventh victim.
With this information, Jason counter-attacked. Her strategy was to disable his main defences and then isolate and remove the required hardware and bioware. Since her weakness lay in her immune system, he used his own probes and released a variety of organic and software viruses, many of which he had encountered during his work and modified.
“Sweetie, don’t you want your mother to live?”
“Given the circumstances, I am on the fence. Couldn’t we discuss this civilly?”
“No, you abandoned me, child.”
“All offspring eventually leave the nest.”
The biggest problem facing Jason in this match was the fact that he was pitted against what amounted to six ILFs. They existed within Segnar and had the collective skill and experience to repel his viruses. He needed a creative approach.
Battle had managed to grab a railing on his way down and had been knocked only slightly silly when he tumbled down the stairs. The conflict between the two machine people was intense. Under his pant leg was a small automatic he had taken to wearing since the hate mail had started. He decided that diplomacy was not going to break up the fight.
Both Jason and Segnar were surprised when 25-calibre heavy-jacketed ammunition began penetrating Segnar. Not being a great shot, Battle concentrated his fifteen rounds in the centre of her mass, with one shot straying into her neck. Normally this sort of injury would take about thirty minutes to repair. However, when Battle was finished, Jason planted one foot and pushed Segnar away, ripping her probes painfully from his neck. With her signals no longer present, he had the capacity to pump her full of every biological toxin and software virus he could think of and synthesize. So much for creativity.
As she lay in a mess of blood and circuitry, she beckoned Jason closer. He did not move. “Say what you want.”
“I never liked you.”
And she was dead.
Jason stood expressionless over her body.
“That was your mother?”
“In a way … her, Intel and Motorola.”
Postlude
December 26, Boxing Day, found Jason Childs and Charles Battle swinging on children’s swings in a snowbound park near the children’s hospital. They had just been delivering post Christmas cheer to the sick and dying children whose families were unable to spend enough time with them over Christmas. Denise Kalef had suggested it – including the elf costumes – as a way for them to come out of the philanthropy closet. Neither Charles nor Jason had ever made a personal appearance to the children they had both helped financially. She said it was time to see the results of their work.
“So,” said Jason, “you thinking of being less anonymous more often?”
Battle got a good swing going and replied, “No. Don’t think so. Nothing beyond this anyway. I really don’t mind my hidden life. There are much worse ones to have. What about you? Your creator is dead; you probably have effective, if not actual, détente with the CIA – considering you let them discover their rogue researcher after all these years.”
“It wouldn’t have happened if you hadn’t lied to them so well over the last two days, particularly about my role in the situation.”
“Whatever. You have a chance to hide less in any case.”
“True. I’ve set up a special message on the Internet for the remaining ILFs. I’m thinking of having a family reunion and then deciding what to do next.”
“Next Christmas I’d like us to do this again, but without me having to shoot anyone and with warmer elf costumes. Interested?”
“Yes, I believe so.”
FIN